Fraud in affiliate marketing is an eyesore of every advertiser. You’re probably more than happy to pay commissions to publishers and affiliates who actually create value for you and your business. But it stings to pay commissions to people who take advantage of your affiliate program by using fraudulent practices. This blog talks about the most common fraud types in affiliate marketing to look out for and also gives a few tips on how to prevent fraud as much as possible.
The most common ways to pay for advertisements are impressions and clicks. It’s not strange that this is also where most of the ad fraud happens. Fraudulent ad impressions and click fraud, CPC, and CPM, are most common. This means you either get fake impressions or fake clicks on your ads, leading to dishonest commission payouts for the fraudster. They can both be executed in one of the following ways.
There are two types of invalid traffic bots. The harmless, General invalid traffic (GIVT) bot. And the harmful Sophisticated invalid traffic (SIVT) bot. The GIVT bots are harmless because their activity is disclosed by the companies that use them. One example is Google, which uses bots to crawl pages and organize indexes. Sophisticated invalid traffic bots, or SIVT bots, are the harmful kind. They are very hard to analyze, identify, and detect. And they can create a lot of false impressions on your ads.
Cookie stuffing or cookie dropping are two terms that describe an affiliate marketing technique where the user receives one or more cookies from another, unrelated, website during a visit to a website without notifying the user. In case of a successfully completed transaction such as buying a product or service, the ‘stuffer’ will receive a commission, while the site that pays hasn’t gained anything.
When someone clicks on a blog via a link to a product in a webshop, this can be a reason to place an affiliate cookie. When two or more cookies are placed, it’s cookie stuffing. When someone visits a site and does not take any active action, cookies can still be placed, in this case, we speak of cookie dropping. Applying this method undermines the commission system because there is no longer a direct line between product and provider. That is why this method is not permitted by most affiliate networks. Offering affiliate cookies via pop-ups on, for example, a review page of a service or product is also a method that usually does not fall within the provider’s guidelines.
You want your traffic to come from actual persons or companies. After all, that’s what you pay for. With this kind of fraud, the traffic derives from a data center. It may look like that target audience that is seeing the ad, but there isn’t a single screen involved. Nobody is actually seeing the ads – so the view shouldn’t be counted.
Here, fraudsters create a blank web page that doesn’t have any content on it. They do add a tech code on the page. The page with the tech code is then added to a low-quality exchange. This way they start generating money through fake impressions. They set the page to redirect to other, similar pages, to create an infinite loop. This creates a lot of fake impressions.
Unfortunately, this kind of fraud is very hard to detect since it falls in the blind spot of most anti-fraud technology.
With click spam, the fraudster executes a click for someone who doesn’t click themselves. Changes are, they haven’t even seen the ad. If you’re being click spammed, your ads probably show an unusually low conversion rate on mobile devices. They create organic traffic by creating clicks on ads that users didn’t make.
This happens a lot in advertisements for apps. If a user clicks an ad and installs the app after a very long time. The click was probably fraudulent.
Click injection is a more sophisticated way of click spamming. They install an app that listens to install broadcasts. This way, it’s possible to detect when other apps are downloaded on the device. This way, the fraudster can trigger clicks before the install is complete and receive credit for the install.
SDK (software development kit) spoofing is also known as traffic spoofing or replay attacks. The fraudster creates fake installs using the data of real devices. This type of fraud is extra harmful because it doesn’t only hurt the publisher, it also hurts the consumer.
There are frequency counters that can detect fraudulent clicks. If the same device ID clicks an ad too many times, it’s counted as fake. To counter this, fraudsters create fake device ID’s. They create a random string of alphanumeric code, a fake device ID. They create a limited amount of fake clicks per ID, so it’s not detected as fraudulent. This drastically increases the CTR.
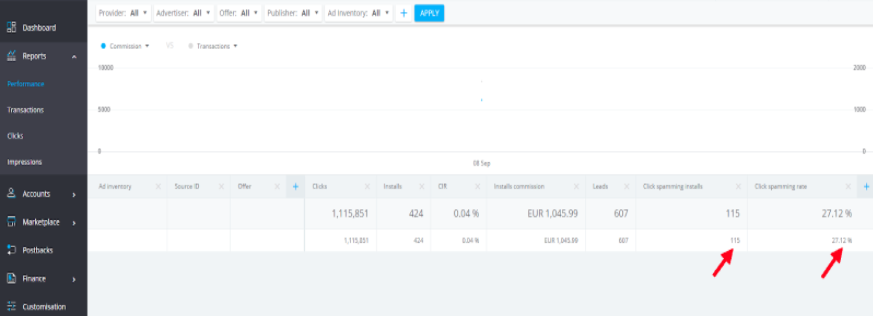
When you use the Target Circle software, you can easily check the performance of the sources for click spamming by logging into your Performance dashboard.
The above image is a clear indication of how you can measure the click spamming installs and rates of your sources. And also if you need a detailed report of per install then you can see that in the transaction report.
There is a constant arms race between fraudsters and detection tools. Each trying to outsmart the other. This means that fraudulent activity is becoming more and more sophisticated and harder to detect. A good example is the ‘I’m not a robot’ click box. It worked great in the beginning, but after a while, fraudsters created bots that mimic human mouse movements that are harder to recognize as fake.
Does that mean there is nothing you can do to prevent fraud? No. It’s always possible to detect fraud by paying attention to a few metrics and by taking steps to limit the impact of fraud on your campaigns.
Abnormal activity is an activity that can’t be rationally explained. If your web traffic suddenly spikes, and you haven’t done anything that could cause that. That’s abnormal activity. Or what if your bounce rate suddenly rises a lot, but you haven’t made any changes to your website. Things like low engagement rates and high click through rates also point to fraudulent activity. It could be caused by bot traffic. It’s wise to start using bot detection tools that can watch out for content-scraping and ad injection.
when you identify a fraudulent publisher or affiliate, be sure to immediately update your blacklist. Always make sure that the list is current, and spend some time communicating the list with partners when rolling out a campaign.